Virtual Private Networks
Virtual Private Networks (VPN) have been utilized by businesses since the early 2000s. They can be complex with auditing and levels of security, or extremely basic with little overhead. The simplest and most commonly used analogy for understanding a VPN is comparing it with a tunnel. A tunnel allows you to start at one location, proceed through the tunnel and arrive at the other side where the tunnel ends. In similar fashion, a VPN allows internet traffic to travel from one location to another, securely – most often traveling from an end user’s work computer to the corporate network and back. It emulates an end user being physically present at their corporate office.
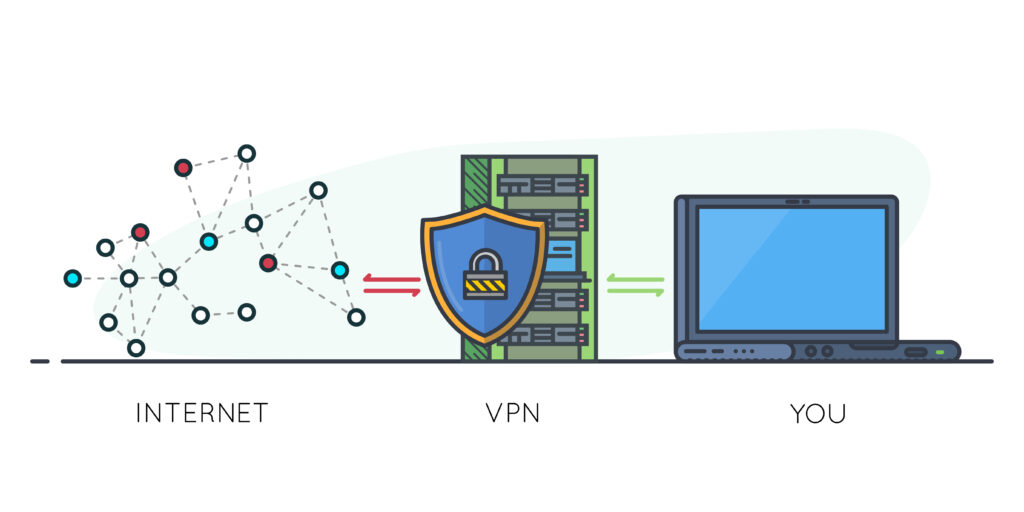
This allows companies to maintain a strong external front (or firewall) facing the internet, and potential threats, while having more of a relaxed stance on internet traffic inside of the company.
Unfortunately, however, this allows more access than is usually necessary. In many instances, a VPN is only used to give a user access to a few corporate apps or files; but unless a company goes through the effort of heavily segregating their network traffic, the VPN gives access to the entire network.
Zero Trust Network Access
Zero Trust Network Access (ZTNA) is a relatively recent concept that handles remote worker access in a new way. Instead of giving the end user total access to the network, ZTNA allows access to only what is needed. Many different vendors and hardware manufacturers have different approaches to the implementation and configuration of ZTNA, but the concepts are similar across the board: more controls over exactly what is allowed to be accessed – and what isn’t. Instead of allowing full access to the network as VPNs do, ZTNA defaults to denying access to all, and only granting access to what is explicitly allowed in the policy.
That isn’t to say ZTNA is the best fit for every organization. There can be significant investment involved in moving to ZTNA (time and money); but it is important to constantly evaluate a company’s IT security and consider best practices.
The old approach to IT and security in the corporate world was to create a moat around the castle and barricade the door; and if you have the key, you can come in and have full access. Now, as the world moves to the cloud, the approach is to start with zero trust and give access to only what is needed – after significant confirmation.
For further questions or clarifications, contact KJK’s Cyber Security & Data Breach team.
